In the world of geopolitics, we probe the weaknesses of those that can hurt us. Not necessarily to attack other parties, but to know these weaknesses – to have them in our back pocket – in case moments of complexity arise, and leverage is necessary. This is the nature of humanity.
On March 5, 2019, major solar and wind asset owner sPower engineers saw “brief communication outages” between their centralized monitoring center and several wind and solar power plants. The company looked further into it and found that the firewall – security hardware used to manage information flows into and out of computer systems – had been rebooting. sPower contacted the hardware manufacturer, Cisco, and found that the reboots were caused by denial of service (DoS) attacks, the practice of overloading computer connections by sending large volumes of data to said connection. These attacks started just after 9 AM MST, and continuing until almost 7 PM MST. The attacks were able to exploit a known vulnerability, and it was soon thereafter patched. No additional attacks have been noted, and sPower stated – after viewing computer logs – that no intrusions were detected.
EE News first reported on the DoS when it occurred. The publisher filed a Freedom of Information (FOI) request for data on the attack, and was recently given this PDF.
There is no public evidence yet suggesting the source of the attacks. As well, sPower says the attack caused no downtime or system issues, other than not being able to see ongoing operations at the site.
But this is definitely not the first time this issue has surfaced. pv magazine USA recently reported on the Federal Energy Regulatory Commission (FERC) is launching a two-part review of U.S. grid cybersecurity, prompted by a 20-month U.S. General Accounting Office (GAO) analysis.
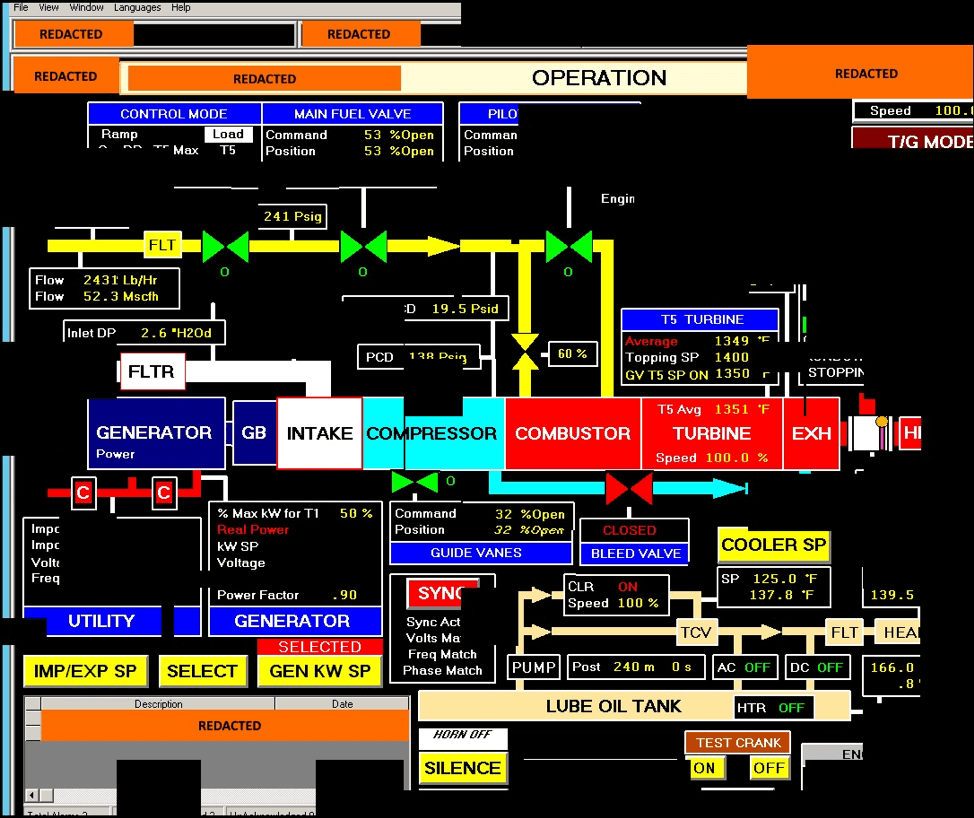
Website Securelink reported on Russian intrusions into the nuclear power industry. The Department of Homeland Security was able to recreate a screenshot (above image) taken by these hackers. It was noted that When exiting systems, Russian actors took efforts to delete applications they used, erase their tracks and clear event logs relating to remote services, audit, and much more.
And while the United States hasn’t publicly stated that any of its hardware has borne physical consequences of a hack, there have absolutely been examples globally. The most well known being the Stuxnet virus aimed at the Iranian nuclear power industry. The virus was able to get into a system disconnected from the internet – in security terms this is called an “air gap” – via memory sticks. It then Targeted the nation’s industrial control systems, infecting over 200,000 computers and caused 1,000 machines to physically degrade.
In Ukraine, during Russia’s invasion of Crimea in order to allow it to hold onto important military bases, tools were deployed allowed hackers to take control of SCADA systems, leading to opened breakers at some 30 distribution substations in the capital city Kiev and western Ivano-Frankivsk region, causing more than 200,000 consumers to lose power.
Recently, the NYTimes recently reported on the deployment of American computer code inside Russia’s grid and other targets.
This content is protected by copyright and may not be reused. If you want to cooperate with us and would like to reuse some of our content, please contact: editors@pv-magazine.com.








A small “factoid” found during the Y2K scare, where among other things old 1960’s code used two numbers for the year such as 64 instead of 1964. It was determined that this alone could crash systems using Point Of Sales World wide. For every “bug” found, there may be several lines of code necessary to set the object code operation “straight”. For every 5 patches, one new “bug” is created. This new bug if not found during testing will create the next weakness in the software for the next attack.
In 2012 Saudi Oil company Aramco was attacked and it took down about 30,000 PCs. Of course recently we have witnessed, if ya’ can’t hack em’ send some drones in to surgically destroy infrastructure.
The bottom line IS and always will be, if you can program it, you can hack it. If you can hack it you can destroy the operating system, control devices to failure or take over and terrorize society from afar. Hardware solutions like, mathematical modeled encryption/decryption or layer after layer of hardware and software protected servers. Then there’s the “cloud”. You don’t know what country this cloud is in, how the servers are protected and who is allowed to buy an account with this “cloud” server that could launch probes from within the cloud on other clients. The typical chess board has 64 squares, there are a lot more possibilities in the real world of computing.
We need mixed power sources and a distributed grid (rooftop solar) along with these large, more cost effective projects.