Energy is one of the top three industries reporting cyber attacks, according to DNV, an independent assurance and risk management provider operating in more than 100 countries. Last year a ransomware attack shut down the Colonial Pipeline, a major supplier of transportation fuel consumed on the East Coast of the United States. The attack by the group Darkside led to soaring prices and panic-buying at the fuel pump until the payment of $4.4 million was made in Bitcoin. How did it happen? It was simply a stolen username and password from the virtual private network that didn’t use multifactor authentication, according to a Bloomberg report.
The Cyber Priority report, released today by DNV, surveyed 948 energy professionals and found that while IT environments are protected, energy businesses need to boost security for its operational technologies (OT), which are the computing and communication systems they use to manage, monitor and control industrial operations. The survey found that fewer than half of the respondents (47%) believe that their OT security is as robust as their IT security and less than one-third of those working with OT believe their company is making securing their supply chain a top priority.
Energy companies have been tackling IT security for several decades. However, securing operational technology (OT) – the computing and communications systems that manage, monitor and control industrial operations – is a more recent and increasingly urgent challenge for the sector. As OT becomes more networked and connected to IT systems, attackers can access and control systems operating critical infrastructure such as power grids, wind farms, pipelines and refineries. Our research finds the energy industry is waking up to the OT security threat, but swifter action must be taken to combat it. Less than half (47%) of energy professionals believe their OT security is as robust as their IT security, said Trond Solberg, Managing Director, Cyber Security, DNV.
The lack of security is not because they are not aware of the possibility of cyberattacks. Four-fifth of the respondents believe a cyberattack on the industry is likely to cause operational shutdowns (85%) and damage to energy assets and critical infrastructure. Three quarters (74%) expect an attack to harm the environment while more than half (57%) anticipate it will cause loss of life.
Russia’s invasion of Ukraine has only heightened the concern for and awareness of the threat. Six in ten C-suite level respondents acknowledge that their organization is more vulnerable to an attack now than it has ever been. However, it appears that some companies are taking a wait-and-see approach before taking action. One explanation for this approach may be that fewer than one quarter (22%) suspect their organization has had a serious breach in the last five years.
“It is concerning to find that some energy firms may be taking a ‘hope for the best’ approach to cyber security rather than actively addressing emerging cyber threats. This draws distinct parallels to the gradual adoption of physical safety practices in the energy industry over the past 50 years,” said Solberg.
DNV recommends that the first step to strengthen defenses is to shore up the supply chain. The Cyber Priority survey reveals that investing in vulnerability discovery must include companies they partner with and procure from.
“Our research identifies ‘remote access to OT systems’ among the top three methods for potential cyber-attacks on the energy industry. We would urge the sector to pay greater attention to assuring that equipment vendors and suppliers demonstrate compliance with security best practice from the earliest stages of procurement,” said Jalal Bouhdada, Founder and CEO at Applied Risk, an industrial cyber-security firm acquired by DNV in 2021.
Balance investment between training and technology
When where their organization is most mature in their cyber security efforts, more than half (59%) pointed more to upgrades to core IT systems and software than they did to training (41%) or the introduction of cyber security expertise (25%). It can be concluded that less focus is dedicated to developing a workforce skilled in understanding and identifying threats, and in detecting and containing attacks.
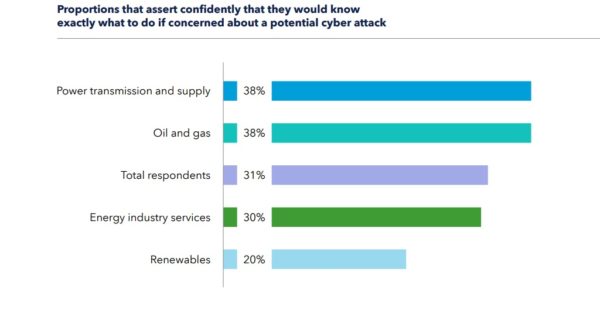
Despite emerging cyber security threats, DNV’s research reveals that less than a third (31%) of energy professionals assert confidently that they know exactly what to do if they were concerned about a potential cyber risk or threat on their organization. This finding points to a need for energy companies to invest in training employees to spot instances of criminal attempts to gain access to their systems
“A company’s workforce is its first line of defense against cyberattacks. Effective workforce training, combined with ensuring you have the right cyber security expertise in place, can make all the difference to safeguarding critical infrastructure. Our research shows a clear need for companies to carefully evaluate their investments in keeping their people well informed of how to identify and respond to incidents in a timely manner,” said Bouhdada.
In the United States, the US Department of Energy (DOE) working to shore up the solar industry’s resilience to cyberattack. In a speech at the State Department in early February, President Joe Biden announced an “urgent initiative” to improve US capability, readiness, and resilience in cyberspace. The Solar Energy Industries Association (SEIA) is continuing its effort to shore up the solar industry’s resilience against cybersecurity threats. SEIA and the Department of Energy Solar Energy Technologies Office (SETO) hosted a half-day virtual summit on the state of cybersecurity in the industry, with emphasis on how these threats must be taken into account from the initial design phase. SunSpec and the Sandia National Laboratories lead a distributed energy resource (DER) Cybersecurity Workgroup to create an industry standard for cybersecurity from the competing frameworks. Interested companies can join the working group to contribute to the development of these critical industry standards and best practices.
Download The Cyber Priority report here.
This content is protected by copyright and may not be reused. If you want to cooperate with us and would like to reuse some of our content, please contact: editors@pv-magazine.com.








By submitting this form you agree to pv magazine using your data for the purposes of publishing your comment.
Your personal data will only be disclosed or otherwise transmitted to third parties for the purposes of spam filtering or if this is necessary for technical maintenance of the website. Any other transfer to third parties will not take place unless this is justified on the basis of applicable data protection regulations or if pv magazine is legally obliged to do so.
You may revoke this consent at any time with effect for the future, in which case your personal data will be deleted immediately. Otherwise, your data will be deleted if pv magazine has processed your request or the purpose of data storage is fulfilled.
Further information on data privacy can be found in our Data Protection Policy.