Alan Mantooth figures that making a $500 fix to a $10,000 piece of equipment could better safeguard the grid from a potentially devastating cyber attack that could be directed at – or even launched by – a solar power plant.
Such an attack on the bulk power system is possible, if unlikely, at least for now.
Mantooth says that safeguards were designed decades ago to offer some measure of cyber security for solar technology. Those safeguard were largely seen as unnecessary, expensive add-ons. After all, the solar industry was laser-focused on driving out costs; an attack through electronic systems was thought to be far-fetched.
Now, however, the realization is growing that cyber threats are real. In a speech at the State Department in early February, President Joe Biden said the government had elevated the status of cyber issues and was launching an “urgent initiative” to improve U.S. capability, readiness, and resilience in cyberspace.
From annoyance to assault
Solar systems of all sizes could pose a risk to the grid in much the same way that an attack on a conventional power plant could result in widespread blackouts. The consequences of a cyberattack could be as minor as reducing a solar array’s power output, or as major as overloading a battery energy storage system to the point of failure. In a worst-case scenario, an intruder could initiate plausible, yet inappropriate commands that disable large portions of the grid.
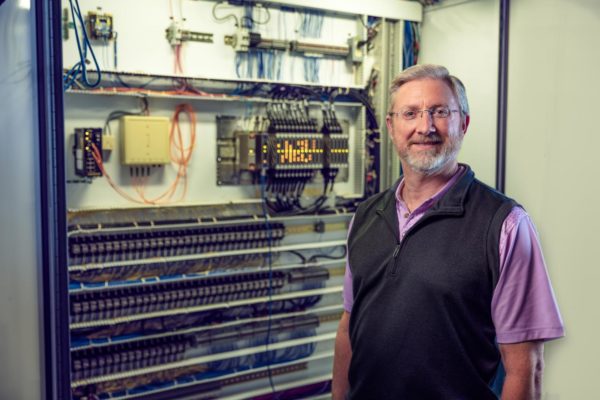
And so, with $3.6 million in grant money from the U.S. Department of Energy Solar Energy Technologies Office, Mantooth and his team at the University of Arkansas’ National Center for Reliable Electric Power Transmission are working to develop sophisticated yet low-cost tools to protect the power electronics housed within inverters, a device that has been given vastly expanded functionality in recent years.
“Inverters represent a vulnerability in the sense that we have to communicate with them,” Mantooth said. The point of contact that enables that two-way communications to occur also means “the grid is vulnerable” to a potential attack.
Where inverters once were used almost exclusively to extract the most power from solar modules and deliver it to a voltage load, today’s technology includes software to enable performance monitoring, ancillary services, and even black start capabilities. More recently, inverters have emerged as central to the growth of virtual power plants, which use software to link together hundreds or thousands of individual inverter-based generation resources and make them available to the distribution grid.
Inverters have grown to be “more intelligent than simply putting out power,” Mantooth said. Indeed, inverters are essentially Internet of Things devices that share their electronics DNA with devices around your house like smart thermostats, TVs, and refrigerators. And like any other Internet-connected device, security breaches can occur.

Mantooth looks at the problem of hardening a solar inverter against a cyber intruder as involving both hardware and software. If no one inserts a hardware trojan horse, then the device can be considered protected, he said.
Software presents a different case. Here, he and his research team assume that a bad actor can access the software that operates an inverter’s power electronics and can manipulate the software to cause harm.
Inverter functionality is addressed under the IEEE 1547 standard, which was revised in 2018 and is currently being rolled out in a range of regulatory rules that cover grid interconnection. Underwriters Laboratories also modified its inverter certification and standard to require voltage ride-through, frequency ride-through, anti-islanding, volt-var, and frequency-watt functionalities, all aimed at improving grid resiliency.
The addition of these kinds of capabilities might also increase cybersecurity vulnerability. The risk may have been compounded by the Federal Energy Regulatory Commission’s Order 2222 of last September. That order opens the door for distributed energy resources to take part in energy markets. While the FERC order was widely hailed for expanding the role that solar can play, it may also broaden the possibility for cyber intrusions.
A lot of damage
Massoud Amin is an IEEE Fellow and professor of Electrical Engineering at the University of Minnesota. He is also widely regarded as the father the smart grid; he led utility security efforts coordinated through the Electric Power Research Institute after the 9/11 attacks. He now warns that a cyber attack targeted against today’s inverters could be “disastrous” in many ways.

“If there’s malware placed in a very large number of devices – not just at the inverters but elsewhere in the system – and they are timed correctly as part of a multi-pronged attack – without giving a blueprint for such an attack, yes, a lot of damage can be done,” Amin said.
Cyber attacks are nothing new. The Stuxnet computer worm was first reported in 2010; it targeted supervisory control and data acquisition systems and was believed to be responsible for causing substantial damage to Iran’s nuclear program.
In 2013, retailer Target’s point of sale databases were hacked, exposing private data on 70 million customers. An investigation found that the hackers had gained access through an HVAC contractor whose password to a vendor portal were stolen.
In what is widely regarded as perhaps the first known successful cyberattack on a power grid, hackers in December 2015 targeted information systems of three energy distribution companies in Ukraine, temporarily disrupting the electricity supply to consumers.
And this past December, a security breach was discovered involving U.S.-based SolarWinds, the network management software of which is widely used across the energy industry. The scale and scope of the breach is still being uncovered, but it could be substantial.
The rise of PEDG
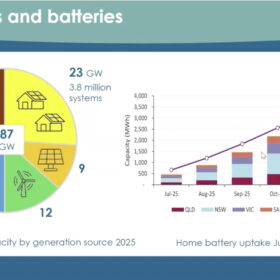
In a 2020 research report, scientists from the National Renewable Energy Laboratory, the University of Illinois-Chicago, and Texas A&M University highlighted grid vulnerabilities as the United States rapidly embraces what they refer to as the electronics dominated grid, or PEDG.
Increased use of PEDG makes the distribution-level grid more vulnerable to cyber-physical attacks. That is because of the sheer number of intelligent devices that can impact power grid stability if compromised.
A typical PEDG includes solar energy generation, flexible loads, local battery systems, smart meters, and so on. All these elements constitute what the researchers refer to as the “device layer” of the cyber-physical system. This layer communicates with a supervisory layer through two-way transfer of information and commands.

NREL
The main role of the supervisory layer, the researchers said, is to assure that the network is operating optimally. It does this by monitoring and controlling device layer entities. But this structure also offers a doorway for attackers who might try to manipulate operations and draw the supervisory control layer into executing incorrect commands.
As one example, the researchers outlined a case in which a grid-following inverter tells the supervisory upper control layer that it is going to island itself due to an internal failure. In response, the control layer acts to inject more power from nearby grid-following inverters in an effort to compensate for the reported generation loss.
However, if a false alarm was sent by a cyber intruder, then the supervisory layer’s action to increase voltage in the distribution network could instead trip overvoltage protection relays, causing a blackout in that portion of the grid. In this way, an otherwise acceptable communication may lead to a blackout affecting thousands of electricity customers.
The researchers wrote that, “with the increased adoption of grid-following inverters in our current energy landscape, their influence and dynamics are crucial in terms of network operation.”

One important point to keep in mind is that if there is no communications link, then little if any cybersecurity vulnerability exists. As explained by Brian Lydic, chief regulatory engineer with the Interstate Renewable Energy Council, the scope and scale of a potential cybersecurity breach depends on the capability of the communications link.
“If settings can be changed over communications, then the potential impact could be larger, limited only by the scope of connected systems,” Lydic said. As inverter-based systems become more widely embedded in grid operations, “we potentially open them up to more vulnerability.”
Despite the increased threat, one possible advantage of bulk power generation from wind and solar is that the systems are composed of many devices coming from a larger and more diverse set of technology providers, said Danish Saleem, a senior Cybersecurity Systems researcher at NREL. “If each device and sensor were to have a mechanism – say, a tripwire – to detect or counter malicious threats, that could support a robust situational awareness and mitigation capability.”
Intrusion detection
Saleem said that NREL is developing metrics to evaluate security at the system-of-systems level. As part of their work, researchers will look at millions of devices, distributed architectures, and their resulting connections under scenarios that can then help determine the potential implications of different types of threats.
It would do this by identifying three operational conditions for each inverter given its location in the network: normal, safe, and abnormal. The proposed IDS, along with other functionalities of smart inverters, would verify that the active and reactive power set points of inverters have not been manipulated.
Layered approach
Meanwhile, back at the University of Arkansas, Alan Mantooth and his team are looking at a multi-layer cyber security approach. One layer would be based on adding a second core processor that would remain “hidden” from view but could be brought online within nanoseconds after an intrusion is detected. The second core processor would take over normal operations and offer protection at what Mantooth says would be a relatively minimal cost, perhaps $500 on a $10,000 inverter.

Image: Enphase
Added to that would be machine learning tools. Here, the power electronics would be taught what constitutes a device’s normal behavior. A related step adds blockchain concepts that enable many inverters to be monitored and evaluated simultaneously. Combined, these security layers “tell us if someone is knocking on our door and if it is legitimate,” Mantooth said.
A more expensive security layer would include a dedicated fiber communications link from a solar facility to a central operations center. That sort of closed communications system would represent an added cost, but also would secure vital communications functions from an external threat.
As a goal, Mantooth says his team aims to produce effective cyber controls that add no more than 15% to the cost of an inverter. And work to date suggests that safeguards will cost “way less than that,” he said. His laboratory’s design solutions are slated to be tested in 2023. For the field demonstration, cyber security devices will be deployed at a 5 MW solar array outfitted with 125 kW string inverters.
Power electronics’ functionality is rapidly evolving and tackling cyber security problem is not a typical engineering problem, Mantooth says. “We have a real adversary where someone is trying to break down my design. We are all learning how to design things better.”
This article was updated March 10, 2021 to correct the spelling of Danish Saleem’s name and credit a study’s co-authorship to the University of Illinois-Chicago.
This content is protected by copyright and may not be reused. If you want to cooperate with us and would like to reuse some of our content, please contact: editors@pv-magazine.com.








Correction.
The author of CyberPELS are from University of Illinois at Chicago and Not University of Chicago.
Thank you for noting the error. I will make the correction.