Most people don’t think about how electricity reaches their homes; they flip a switch and a light turns on. But behind that simple action is a vast network of power plants, conductors, sensors and control rooms that stretches across the United States. This is the electric grid, and it is responsible for delivering electricity to nearly every home and business in the country.
For much of its history, the grid operated in a straightforward way. Large power plants generated electricity, which then moved in one direction from the power plant, through transmission lines to neighborhoods and cities. The equipment that controlled this process was built for a closed environment in an analog era.
Over the past decade, the U.S. energy landscape has shifted dramatically as electricity increasingly comes from distributed energy resources (DERs) such as rooftop solar, residential energy storage systems and electric vehicles capable of feeding power back to the grid. These technologies rely on constant digital communication with each other and the grid, creating a level of real-time interconnection the grid system was never designed to handle. While this decentralization improves resilience and supports decarbonization, the integration of millions of internet‑connected devices has also introduced significant cybersecurity vulnerabilities.
In 2015, attackers found a way into the digital tools that operators in Ukraine used to run the power system and shut off electricity to hundreds of thousands of people in the middle of winter. The U.S. has also seen critical infrastructure targeted, with cyberattacks on utilities increasing 75% from 2023-2024. The lesson is clear: Exposed digital systems can be exploited to cause real‑world disruption.
As newer, DERs become integrated into everyday grid operations, their secure performance becomes essential. The strength of the modern electric system now depends as much on the reliability of its digital components as on its physical ones. Protecting these systems is critical to ensuring that electricity remains stable, dependable and available when people need it.
How local energy resources are reshaping the grid
Because DERs are located close to the homes and businesses that use their electricity, they reduce transmission losses and make energy delivery more efficient. They also shift the grid away from dependence on a small number of large power plants and toward millions of smaller devices generating and managing electricity in real time, which can help keep electricity flowing even if individual components fail.
Many of these devices operate using inverter‑based resources, or IBRs, which have become essential to modern grid stability. These inverters convert the direct current produced by technologies such as solar panels and batteries into the alternating current used in commercial and residential buildings, but their role extends far beyond that basic function.
Today’s inverters actively regulate voltage, adjust power output and help correct fluctuations on the network. If the control settings on even one device are misconfigured — or deliberately altered — conditions like overvoltage can occur. That’s when electricity flows at levels higher than equipment is designed to handle. Backfeeding, where power moves in the wrong direction, is another risk. These issues can strain equipment, damage components or trigger failures that ripple outward.
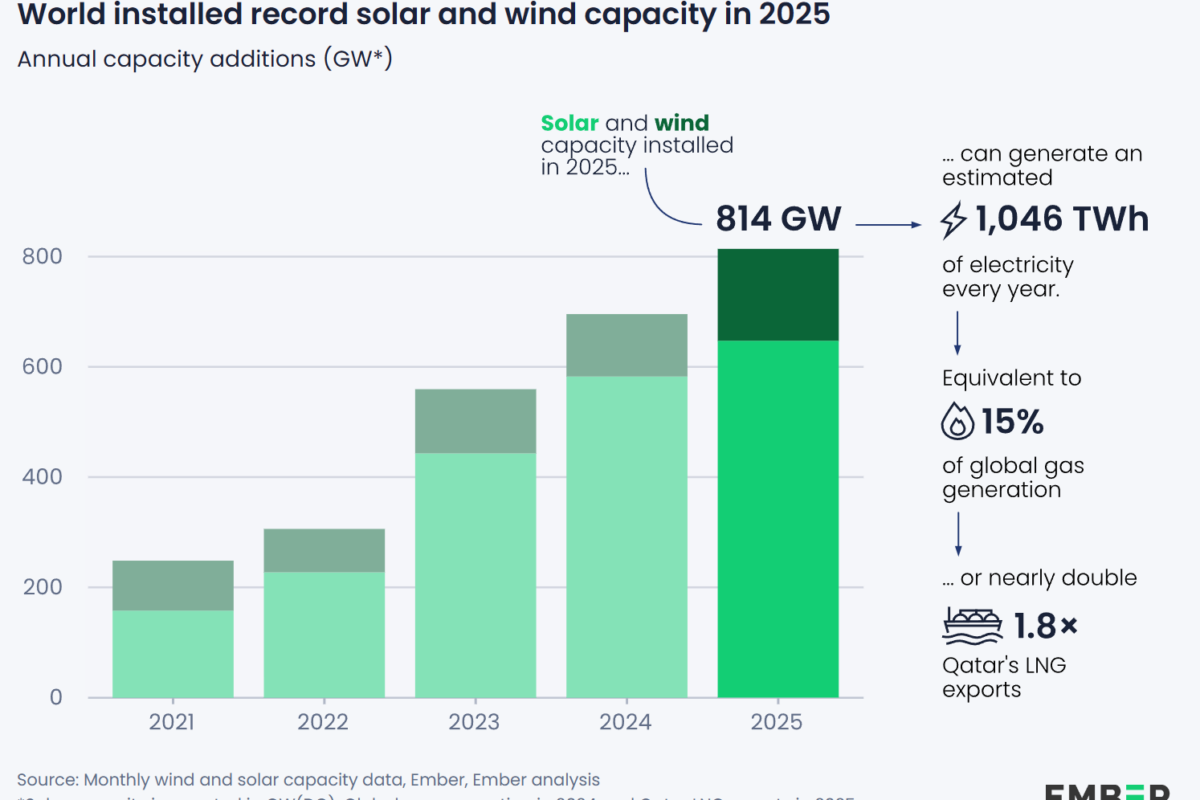
Renewable energy is projected to supply about 45% of U.S. electricity by 2030, up from roughly 22 to 23% today. As adoption continues to grow, the grid increasingly depends on DERs and IBRs to support stable operation. Because these devices now play such a central role, their secure and reliable performance has become integral to maintaining a resilient electricity system.
When modern grid technology creates new vulnerabilities
The rapid proliferation of DERs has introduced new expectations for cybersecurity that many existing devices were never built to meet. For decades, features like strong authentication, encrypted data exchange or regular software updates were rarely required. Now that these devices connect to networks, the absence of these protections can leave them exposed to unauthorized access. Without uniform protections, even routine communication between devices can become a potential weak point.
A central challenge is that existing cybersecurity standards have not yet been broadly adopted or tailored to the unique requirements of DERs and IBRs. Existing standards, such as NERC CIP, were designed for isolated, centralized systems, and lack essential security features like encryption when exposed to the internet. As states across the country adopt ambitious renewable energy goals and utilities rely more on DERs and IBRs to stabilize the grid, this lag in security development is critical because the attack surface is expanding rapidly.
Closing the cybersecurity gap will require proactive collaboration across the energy sector. Strong protections — such as authentication, authorization, encryption and so on — need to be built into both hardware and software from the start. Establishing clear, widely accepted requirements will help ensure that all devices, regardless of manufacturer or deployment, can operate securely within a more interconnected and digital controlled grid.
Designing distributed energy systems with security in mind
The number of devices involved in managing electricity continues to grow, and many of them perform functions that directly affect how power flows. To keep these systems dependable, cybersecurity must be embedded during the design phase of DER and IBR devices.
One effort that supports this need is UL 2941, the standard for Cybersecurity of Distributed Energy and Inverter-Based Resources. It provides a framework to evaluate whether DERs meet certain cybersecurity expectations and helps customers understand how devices align with those requirements. UL 2941 focuses on network‑connected, endpoint devices that manage significant energy flows and that could, in large numbers, create aggregated risk to grid stability. It also offers comprehensive cyber‑related requirements meant to help safeguard energy systems against threats and support secure, reliable operation.
As a result, renewable energy providers can specify and/or use well-defined and scientifically proven requirements to demonstrate compliance. Utilities and integrators gain confidence that devices they adopt follow a consistent approach to security. And at the industry level, shared expectations help establish a baseline for resilience, consistency and consensus as more DERs and IBRs come online. By pairing security‑by‑design with clear, standardized guidance, the energy sector can scale distributed resources in a way that supports both energy goals and secure grid operation.
Strengthening reliability as decentralized energy grows
Distributed energy changes not just how power is generated, but how it must be managed, and safeguarding those systems is now a core part of supporting decentralized energy. Cybersecurity should be considered as fundamental as voltage regulation and frequency control. Protecting digital components is now an essential part of keeping electricity dependable.
Moving in this direction will take coordinated effort. Manufacturers, utilities, code authorities and standards bodies all have a role in establishing consistent expectations for device security. Shared frameworks — such as those developed to evaluate the cybersecurity of DERs and IBRs like UL 2941 — offer a blueprint to create more uniform protections that support reliable deployment at scale. When security expectations vary widely, the entire system becomes harder to manage; when expectations are aligned, reliability strengthens.
Ultimately, protecting the future of energy means designing systems that are not only connected and efficient, but also secure and dependable. Incorporating cybersecurity into distributed technologies today helps ensure they continue to function correctly as they expand. The only effective time to address these needs is before a disruption or attack occurs — not afterward.
Michael Slowinske: Senior Director & Regional GM (Americas), UL Solutions Michael leads engineering and sales for the Energy and Industrial Automation division. With 30 years of experience, he has managed engineering operations and served on international standards committees. He previously served as Director of Principal Engineering, focusing on emerging technology safety. A licensed Professional Engineer, Michael holds an Environmental Engineering degree from Washington University and an MBA from Northwestern’s Kellogg School.
Sjoerd Willemsen: Principal Engineer, UL Solutions Based in Arnhem, Netherlands, Sjoerd specializes in cybersecurity and interoperability for power systems and industrial communication. He holds a degree in Embedded Systems Automation and actively contributes to several IEC committees, including TC 57 (power systems management) and TC 2941 (DER cybersecurity). He also addresses digital innovation and the Metaverse through IEC/ISO JSEG 15.
The views and opinions expressed in this article are the author’s own, and do not necessarily reflect those held by pv magazine.
This content is protected by copyright and may not be reused. If you want to cooperate with us and would like to reuse some of our content, please contact: editors@pv-magazine.com.






By submitting this form you agree to pv magazine using your data for the purposes of publishing your comment.
Your personal data will only be disclosed or otherwise transmitted to third parties for the purposes of spam filtering or if this is necessary for technical maintenance of the website. Any other transfer to third parties will not take place unless this is justified on the basis of applicable data protection regulations or if pv magazine is legally obliged to do so.
You may revoke this consent at any time with effect for the future, in which case your personal data will be deleted immediately. Otherwise, your data will be deleted if pv magazine has processed your request or the purpose of data storage is fulfilled.
Further information on data privacy can be found in our Data Protection Policy.