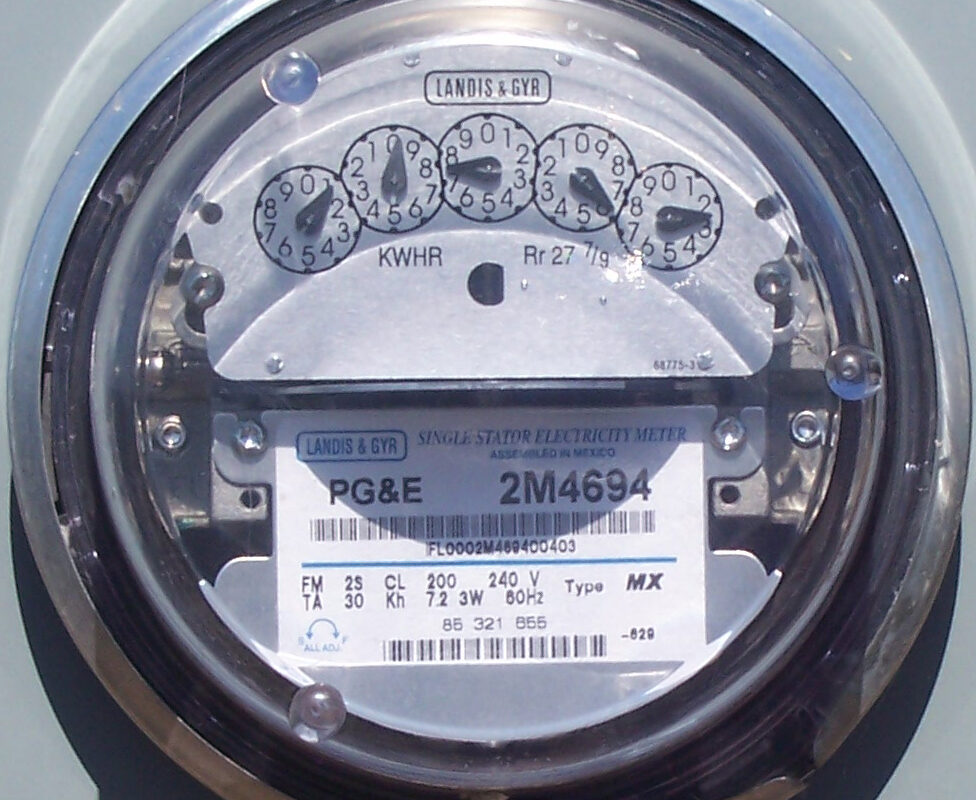
Cybersecurity is a critical concern for utility-scale energy storage systems (ESS). Though ESS can serve as valuable sources of back-up power that boost grid reliability, their complexity is opening new doors for cyberthreats.
A recent webinar hosted by the Clean Energy States Alliance (CESA) and the Energy Storage Technology Advancement Partnership discussed the key security risks faced by ESS and outlined some best practices. Moderated by Todd Olinsky-Paul, CESA’s senior project director for energy storage, the webinar included speakers from the North American Electric Reliability Corporation (NERC) and the Electric Power Research Institute (EPRI).
“As the scale of battery storage grows, their fundamental functionality remains the same,” explained Sai Ram Ganti, a cybersecurity specialist at EPRI. “Though larger batteries have a greater impact on the grid, the only thing that changes from a cybersecurity perspective is the complexity in the electronics.”
He added that larger projects require sophisticated charge/discharge cycles, protection mechanisms and monitoring systems, all of which introduce vulnerability.
Ganti also pointed to third-party vendor integration and remote access solutions as major risk factors for cyberthreats. The more components involved in producing an ESS, the higher the overall security risk.
“Cybersecurity not only deals with protection against bad situations but also against humans,” said Howard Gugel, the senior vice president of regulatory oversight at NERC. “From source to installation, there are a lot of hands that touch the product.”
“Having a compromise occur at some point in that chain is a concern too,” he added.
Many vendors want remote access to ESS information like battery health data for analytical or warranty-related purposes. But that bumps up the potential for cyber intrusion, meaning strict authentication and monitoring are essential. Plus, due to limited processing power, it’s often difficult to assess an ESS’ security in real-time while the systems are still online. And cybersecurity protocols aren’t universal between utilities and vendors.
Data security is also a pressing issue.
“With many platforms connecting to cloud systems, operational data is increasingly exposed to cyberthreats,” Ganti said. Growing usage of cloud-based management tools means that data security must extend beyond physical infrastructure to include robust encryption and access controls, though physically securing the systems is also crucial.
Panelists noted that though security models for ESS vary, they all present risks.
In one model, the utility owns the system while vendors have read-only access for analytics and warranty verification; Ganti noted that this approach reduces risk but “still requires strict controls” to prevent data breaches.
In another model, vendors retain operational control, necessitating rigorous safeguards against unauthorized access.
Regardless of the approach, panelists agreed, cybersecure best practices include segmenting system components into electronic security zones, monitoring east-west network traffic, preventing spoofed sensor data and maintaining whitelists for critical assets.
“Baseline network traffic analysis is crucial for detecting anomalies before they become threats,” Ganti emphasized.
From a regulatory standpoint, Gugel stressed the need for standardized cybersecurity measures to avoid widespread outages; he also highlighted proactive measures including supply chain risk assessments and silicon verification.
This content is protected by copyright and may not be reused. If you want to cooperate with us and would like to reuse some of our content, please contact: editors@pv-magazine.com.







By submitting this form you agree to pv magazine using your data for the purposes of publishing your comment.
Your personal data will only be disclosed or otherwise transmitted to third parties for the purposes of spam filtering or if this is necessary for technical maintenance of the website. Any other transfer to third parties will not take place unless this is justified on the basis of applicable data protection regulations or if pv magazine is legally obliged to do so.
You may revoke this consent at any time with effect for the future, in which case your personal data will be deleted immediately. Otherwise, your data will be deleted if pv magazine has processed your request or the purpose of data storage is fulfilled.
Further information on data privacy can be found in our Data Protection Policy.